this post was submitted on 28 Sep 2023
324 points (75.7% liked)
Games
34539 readers
674 users here now

Welcome to the largest gaming community on Lemmy! Discussion for all kinds of games. Video games, tabletop games, card games etc.
Weekly Threads:
Rules:
-
Submissions have to be related to games
-
No bigotry or harassment, be civil
-
No excessive self-promotion
-
Stay on-topic; no memes, funny videos, giveaways, reposts, or low-effort posts
-
Mark Spoilers and NSFW
-
No linking to piracy
More information about the community rules can be found here.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
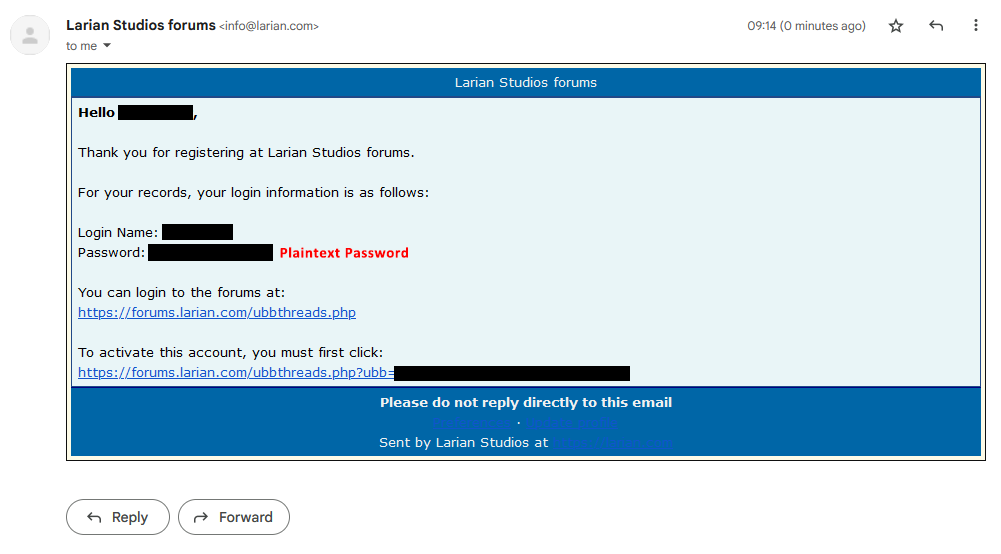
Yes, still not worth risking using a duplicate password though.
Honestly, why risk duplicate passwords even then? I have one strong password that I use for accessing my password manager, and let the password manager generate unique random passwords. Even if I had an easier password that I duplicated with some small changes, I'd still use a password manager to autofill it anyway. I use bitwarden personally, you can also self host it with vaultwarden but it seemed like more trouble than it was worth imo
This is a friendly reminder to everyone that password managers are not risk free either. LastPass was hacked last year, NortonLifeLock earlier this year.
Personally the risk of bitwarden is outweighed by its convenience (compared to self hosted/local only solutions) in my opinion, but I know that'll change real quick if bitwarden ever has a breach. If it does I'm jumping ship to a self hosted or local only solution, but I'm hoping that doesn't have to happen
Bitwarden is end to end encrypted. If the host gets hacked your passwords are still as safe as your master password is. Self hosting wouldn’t really be a huge help there. Possibly even detrimental depending on your level of competence at securing a public facing web host.
They're as safe as your master password is...and as the encryption is. LastPass famously got hacked recently, and in the aftermath of that many users noticed that their vault was encrypted using very small numbers of rounds of PBKDF2. The recommended number of rounds had increased, but LastPass left the number actually used too low for some users, rather than automatically increasing it. Users of Bitwarden and any other password vault should ensure that their vault is using the strongest encryption available.
Well, self-hosting makes you a smaller target. The most determined attackers are likely going to go after the biggest target, which is going to be a centralised service with thousands of users' vaults. If you host it yourself they probably won't even know it exists, so unless there's reason for someone to be specifically targeting you (e.g. you're a public figure), or you get hacked by some broad untargeted attack, you might be better off self-hosted from a purely security standpoint.
(That said, I still use centrally-hosted Bitwarden. The convenience is worth it to me.)
You’re underestimating the attack surface of a self hosted set up. You don’t need to be specifically targeted if, for instance, someone hacks the Bitwarden docker image you’re using, or slips a malicious link into a tutorial you’re reading. It’s not a set it and forget it solution either, you’re responsible for updating it, and the host OS. Like I said, depending on your competency, it’s not inherently more secure.
I heard people’s LastPass accounts were getting compromised after that theft, but I also don’t know how strong their master passwords were.
Yeah at this point it's considered likely that LastPass vaults are being cracked, based on LP being the common link between various other accounts that are being breeched.
A small number of rounds of encryption being the default for users with old enough accounts is believed to be a significant part of the issue. It means even if their password was a good one, the vault can be brute forced comparatively quickly.
If their password was actually good (18+ random characters) it's not feasible with current day technology to brute force, no matter how few PBKDF2 iterations were used.
Obviously it's still a big issue because in many cases people don't use strong enough passwords (and apparently LastPass stored some of the information in plaintext) but a strong password is still good protection provided the encryption algorithm doesn't have any known exploitable weaknesses.
Centralized, third party password managers, yes. Local-only managers like KeepassXC though, no concerns over some company getting hacked or cheeky
This is why I don't use a common centralized password manager, just like I don't use any of the most popular remote desktop solutions like TeamViewer for unattended access.
I run a consumer copy of Pleasant Password Manager out of AWS and use NoMachine for unattended access to any machines where I need it.
Security through obscurity is tried and true. Put as little of your security attack surface in the hands of others as is reasonable.
Applies to every site ever