this post was submitted on 20 Oct 2024
424 points (98.8% liked)
Piracy: ꜱᴀɪʟ ᴛʜᴇ ʜɪɢʜ ꜱᴇᴀꜱ
61888 readers
420 users here now
⚓ Dedicated to the discussion of digital piracy, including ethical problems and legal advancements.
Rules • Full Version
1. Posts must be related to the discussion of digital piracy
2. Don't request invites, trade, sell, or self-promote
3. Don't request or link to specific pirated titles, including DMs
4. Don't submit low-quality posts, be entitled, or harass others
Loot, Pillage, & Plunder
📜 c/Piracy Wiki (Community Edition):
🏴☠️ Other communities
FUCK ADOBE!
Torrenting/P2P:
Gaming:
💰 Please help cover server costs.
 |
 |
|---|---|
| Ko-fi | Liberapay |
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments

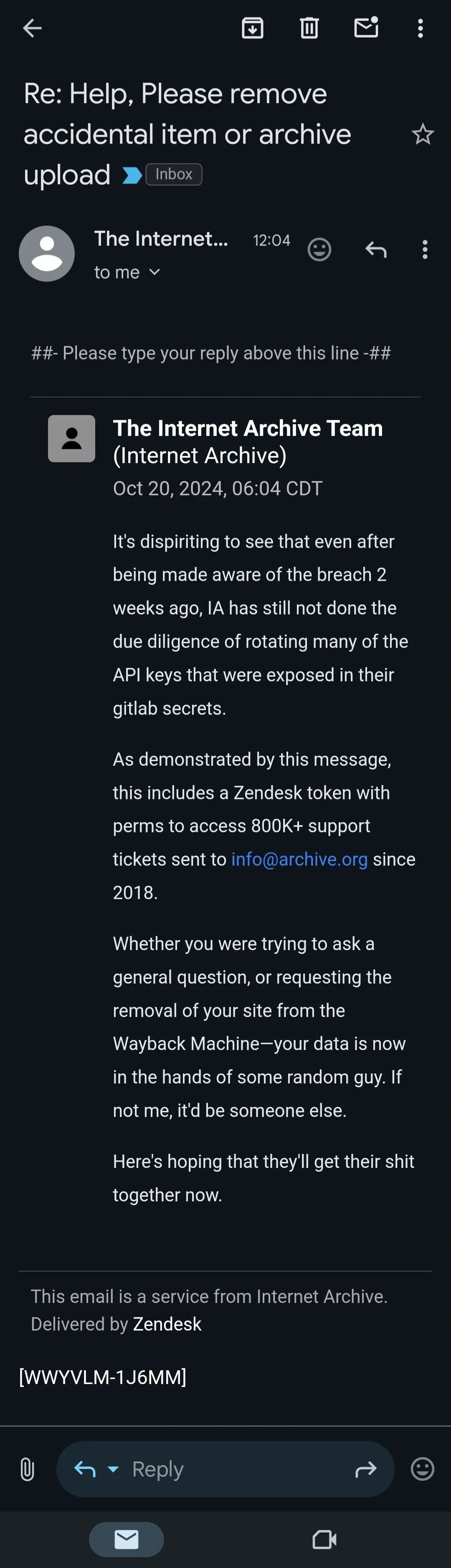
This guy is outing the archive for terrible security posture by bringing attention to it because they received disclosures and did not fix them.
Don't get shit twisted - he's the hero here. IA fucked up and has been vulnerable to manipulation by any number of corporate or national actors this entire time.
If this was genuinely done out of love I could understand but due to the legal battles the internet archive is currently being dragged through, I harbor suspicion of their intent.
If they were really "the hero", they'd follow the bare minimum of responsible disclosure best practices, and allow 90 days between privately alerting them of the issue and going public with it. Two weeks is absurd.
90 days to cycle private tokens/keys?
90 days is just the standard timeframe for responsible disclosure. And normally that's just a baseline with additional time being given if there's genuine communication going on and signs they're addressing the problem.
90 days is standard for "you're code is fucked when someone presses this..."; if the issue is Dave left the keys in the parking lot and someone copied them, two weeks is more than enough time for them to recieve the notice, create a ticket to rotate the keys and a ticket to trigger an investigation (gotta document anytime an org fucks up so it doesn't happen again, right?). Maybe I'm over simplifying it though, I don't know how their org operates.
I agree in general, but
This is exactly why just sticking to the 90 day standard is better. For the supposed security researcher it's a CYA move at worst.
You don't leak a passwords database publicly on the Internet in good faith.
Not necessarily the same hacker.
Are you saying the person who sent the zendesk email is going to try to get IA to hire them for something? I'm not sure I follow...
Still not sure what you're talking about.. Is someone going to ask IA for payment related to the zendesk email?
Thanks for clarifying.
You sure about that, or are you hypothesizing?
There's never certainty when talking about hackers...
That's verbatim the content of the email and the email hack does not appear to be malicious (unlike the ddos or the password breach)
It's more likely that this is 3 different groups than it is a single group.