this post was submitted on 08 Oct 2023
779 points (98.6% liked)
Programmer Humor
36860 readers
11 users here now
Post funny things about programming here! (Or just rant about your favourite programming language.)
Rules:
- Posts must be relevant to programming, programmers, or computer science.
- No NSFW content.
- Jokes must be in good taste. No hate speech, bigotry, etc.
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
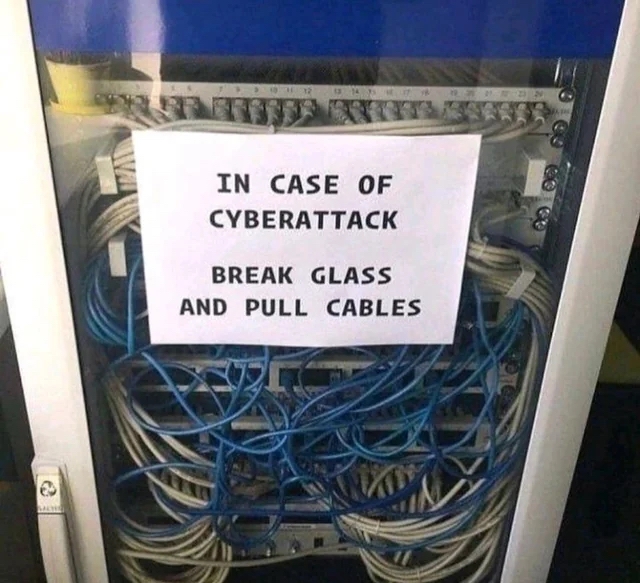
Uh no
Go to the main breaker that feed the servers whatever. And pull the 600v switch off
The smartest layout for that situation is having the main breaker box close to the hooman IT operator room
No choice if it is very serious breach
Nah. Rip that shit right out of the chassis. Destroy that RJ45 port. Make it so the security audit team has to resolder a jack to the mobo before they can even ssh to the box.
Trust me I run a security company. If you need help with your security please feel free to contact me! We are the best in the business!
Yea but it take time !!!
How many shit you have to unhook from whatever to save the shit ?? 100 ?? That take minutes !!!!!
just have a tub of water rigged above the server
Y'all... just... unhook the cable from the demarc...?
The advice I've always heard is disconnect network but leave powered for forensics/recovery. Some ransomware store the decryption key soley in memory, so it is lost upon power loss
That actually makes sense. We had a ransomware attack once. We also disconnected the device but I cant remember if we powered it off. At the time it stopped encrypting due to that since our network drives were not reachable anymore.
Is there actually a way to spread the encryption process to a server?
Im not a it expert at alll. But reallly ?
Best I understand the encryption key is needed to encrypt and decrypt, so if the malware isn't written well enough it may well continue to store the encryption key in memory.
There's some old malware on archive.org that just pulls the FAT off the filesystem into memory and offers a dice roll to restore it
Depending on where the breaker is relative to the UPS, of course.
I vaguely remember the advice actually being to leave it running but disconnect it from the internet. Although maybe hard disconnect the backups if you can.
And probably the intranet, too, just to be safe.
Should be a trunk line disconnect switch that kills both power and data. And if your manager is cool, then it's a guillotine switch.
No, have a Safety Control Rod Axe Man. The dropping rod hits the breakers and smashes it, cutting power!