So i've been hosting a modded Minecraft server for my friends and me on weekends. While it's been a blast, I've noticed that our current setup using LAN has its limitations. My friends have been eagerly waiting for their next "fix" (i.e., when they can get back online), and I've been replying with a consistent answer: this Friday.
However, exploring cloud providers to spin up a replica of my beloved "Dog Town" Server was a costly endeavor, at least for a setup that's close to my current configuration. As a result, I've turned my attention to self-hosting a Minecraft server on my local network and configuring port forwarding.
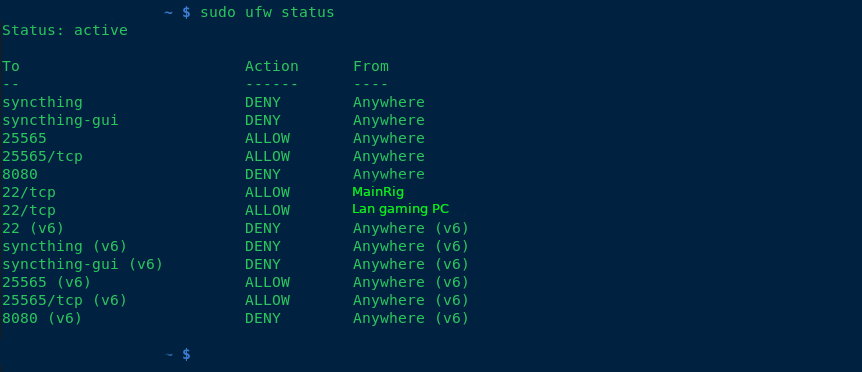
To harden my server, I've implemented the following measures:
- Added ufw (Uncomplicated Firewall) for enhanced security.
- Blocked all SSH connections except for the IP addresses of my main PC and LAN rig.
- Enabled SSH public key authentication only.
- Rebuilt all packages using a hardened GCC compiler.
- Disabled root access via
/etc/passwd. - Created two users: one with sudo privileges, allowing full access; the other with limited permissions to run a specific script (
./run.sh) for starting the server.
Additionally, I've set up a fcron job (a job scheduler) as disabled root, which synchronizes my Minecraft server with four folders at the following intervals: 1 hour, 30 minutes, 10 minutes, and 1 day. This ensures that any mods we use are properly synced in case of issues.
any suggestions of making the computer any more secure, aswell as backup solutions? thanks!
--edit Im using openRc as my init system and my networking plan, is to have dogtown on a vlan via my 48port switch.
--added note, what hostnames do you guys call your servers? I used my favorite band albums and singles for hostnames.
--update Used tailscale, were all addicted to the create mod. And its all been working flawlessly. THANK FOR THE SUGGESTIONS SMART INTERNET PEOPLE!

So the local machine doesn't really need the firewall; it definitely doesn't hurt, but your router should be covering this via port forwarding (ipv4) or just straight up firewall rules (ipv6).
You can basically go two routes to reasonable harden the system IMO. You can either just set up a user without administrative privileges and use something like a systemd system level service to start the server as that user and provide control over it from other users ... OR ... if you're really paranoid, use a virtual machine and forward the port from the host machine into the VM.
A lot of what you're doing is ... fine stuff to do, but it's not really going to help much (e.g. building system packages with hardening flags is good, but it only helps if those packages are actually part of the attack surface or rather what's exposed to the remote users in someway).
Your biggest risk is going to be plugins that aren't vetted doing bad things (and really only the VM or using the dedicated user account provides an insulation layer there -- the VM really only adds protection against privilege escalation which is pretty hard to pull off on a patched system).
My advice for most people:
For Minecraft in particular, to properly back things up on a busy server you need to disable auto save, manually force save, do the backup and then enable auto save again after your backup. Kopia can issue commands to talk to the server to do that, but you need a plugin that can react to those commands running on the server (or possibly to use the server console via stdin). Realistically though, that's overkill and you'll be just fine backing up the files exactly as they are periodically.
Kopia in particular will do well here because of its deduplication of baked up data + chunking algorithm that breaks up files. That has saved me a crazy amount of storage vs other solutions I've tried. Kopia level compression isn't needed because the Minecraft region files themselves are already highly compressed.