Oh man, total flashback to when I did this for Owncloud https://github.com/Fmstrat/shorten
Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
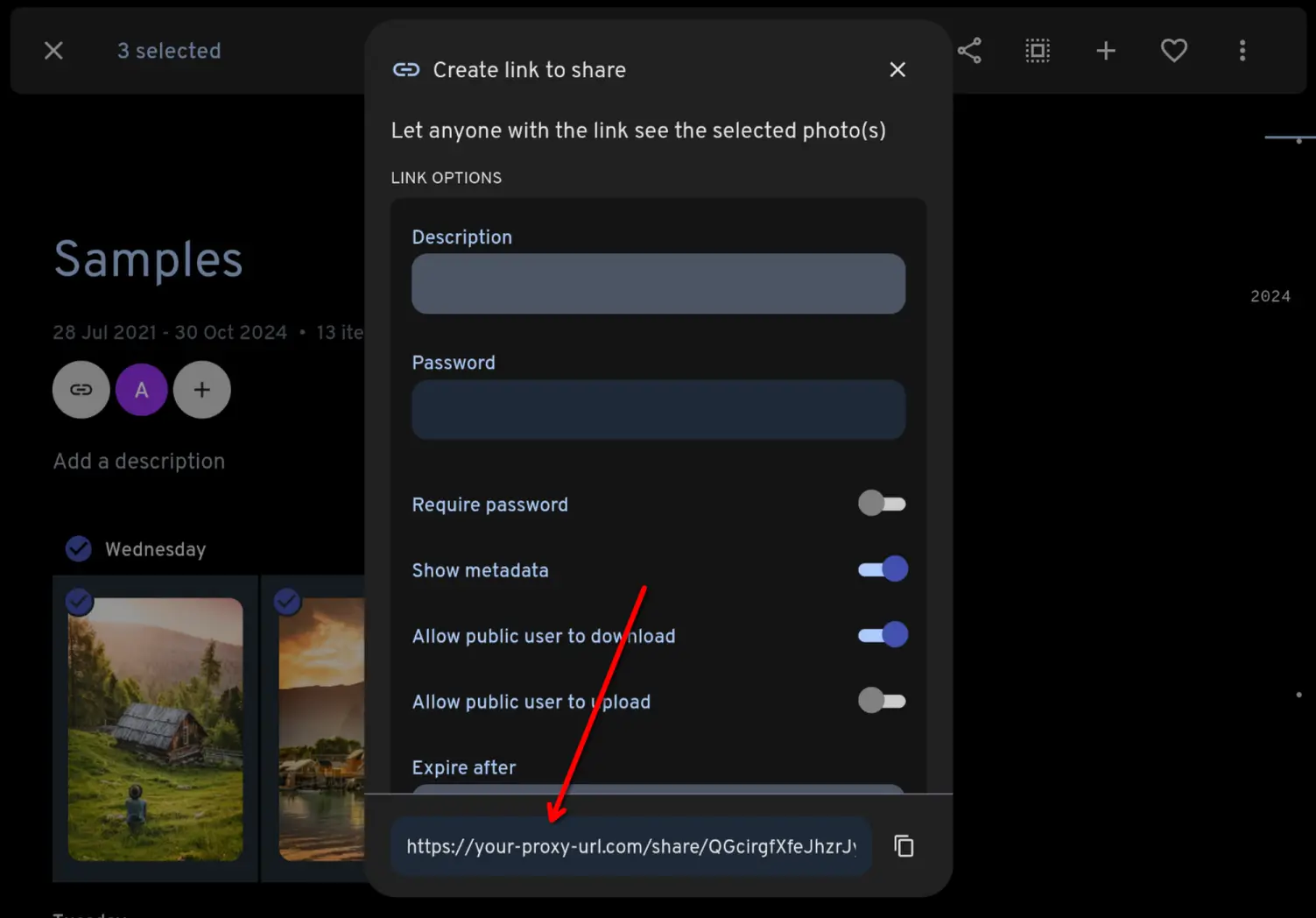
You can see [a live demo here](https://immich-demo.note.sx/share/ffSw63qnIYMtpmg0RNvOui0Dpio7BbxsObjvH8YZaobIjIAzl5n7zTX5d6EDHdOYEvo), which is serving a gallery straight out of my own Immich instance.
Sorry, off topic, but is this what Immich looks like out of the box, or have you used any other plugins?
Immich Public Proxy looks like exactly what I want for my family photos, but I haven't looked into Immich yet. The demo looks beautiful, and is simple enough for the grandparents to use 🙂
Sorry, off topic, but is this what Immich looks like out of the box, or have you used any other plugins?
No - this is using lightGallery. You can see what Immich looks like on their demo.
Thank you 🙂
Immich on its own looks good, but if I set it up, I think I'll definitely install lightGallery to go with it 🙂
Not default but can highly reccommend immich its great.
Thanks 🙂
Okay...I'm terribly confused by this project here, so maybe you can clarify some things.
First, looking through the code, it seems you're literally just taking input requests and replaying them to a target host. So if Immich is updated with changes that proxy doesn't have yet, everything breaks.
How is this adding more security than any other proxy?
You're correct - it is indeed taking input requests and requesting the related data from Immich.
How is this adding more security than any other proxy?
To allow sharing with Immich using a normal reverse proxy like Caddy or Traefik, you need to expose public access to the Immich /api/ path, along with a few other potentially dangerous paths. Any existing or future vulnerability has the potential to compromise your Immich instance.
This proxy is more secure as it does not allow public access to the Immich API path or to any Immich path. The only incoming requests which are honoured are requests like this:
https://your-proxy-url.com/share/ffSw63qnIYMtpmg0RNvOui0Dpio7BbxsObjvH8YZaobIjIAzl5n7zTX5d6EDHdOYEvo
If the shared link does not resolve to something that you have intentionally shared from Immich, it will return a 404.
if Immich is updated with changes that proxy doesn’t have yet, everything breaks.
The only thing which would break it is if Immich changed the format of a few select API endpoints. And if that ever happens it's a very easy fix.
Or you could similar just block those routes in whatever reverse proxy you'd use out in front of the server?
I don't run Immich myself, but just trying to understand the technical issues and this particular solution. Seems like they should have a public facing /shared route that doesn't require access to any others, so I see your point.
Or you could similar just block those routes in whatever reverse proxy you’d use out in front of the server?
You can't. You need to allow public access to your Immich instance's /api/ path to use Immich's built-in sharing.
A simpler way to protect a private service with a reverse proxy is to only forward HTTP GET requests and only for specific paths.
It’s extremely difficult to attack a service with only GET requests.
The security of which URLS are accessible without authentication would be up to immich.
I don't know the Immich API, but I've seen several REST APIs that used the usual pattern of
GET /api/v1/user/<id> - read user
POST /api/v1/user/ - create user
...
but also allowed
GET /api/v1/user/<id> - read user
GET /api/v1/user/?action=create - create user
...
Yup, also some APIs use GET for everything. It's a pain. And it means that filtering by verb only helps if you're intimately familiar with the API. And even then, only if you keep up with changes as they happen. So really, only if you're developing the API yourself.
(another pet peeve of mine is "rest" APIs that use 200 response codes for everything)
Ahhhhh whyyyyy, you've got all of these standard response codes made for you, why would you blatantly ignore them like that?!
The only one I think is reasonable is GraphQL. But that isn't rest, and HTTP is just one of the transport layers it supports.
For anything claiming to be RESTful, it's a crime.
Yes, there are broken uses of the HTTP protocol verbs where filtering to GET won’t work.
The security of which URLS are accessible without authentication would be up to immich.
This is exactly the risk I'm wanting to mitigate. Immich is under heavy active development, and I want to abstract away from needing to worry whether the no-auth API URLs are safe to expose publicly.
At the end of the day I feel safer knowing that there is zero public access to any part of my Immich instance, which for me is what really matters.
Immich has a whole set of end-to-end automated tests to ensure they don't accidentally make public any URLs they went to be private:
https://github.com/immich-app/immich/tree/main/e2e/src/api/specs
As a popular open source project, that would be e glaring security hole.
Using this proxy puts the trust in a far less popular project with fewer eyeballs on it, and introduces new risks that the author's Github account is hacked or there's vulnerability in he supply chain of this docker container.
It's also not true that you "never need to touch it again" . It's based on Node whose security update expire every two years. New image should be built at least every two years to keep to update with the latest Node security updates, which have often been in their HTTP/HTTPS protocol implementations, so they affect a range of Node apps directly exposed to the internet.
All good points, and Apple has some of the most skilled engineers in the world and The Fappening still happened.
It's not possible for me to audit everything that's happening security-wise in Immich, but I can fully understand what's happening in this small codebase to my own satisfaction. At the end of the day I feel safer knowing that there is no public access to any part of my Immich instance.
It’s also not true that you “never need to touch it again”
I meant that you don't need to use it to share photos, not that you never need to update your docker containers! 😱 Thanks, I have clarified that.
Interestingly the recent D-Link NAS security flaw uses GET.
Good example. It’s true that an even a GET request not designed to mutate data might still fail to validate input, allowing a SQL injection attack or other attack that escalates to the privileges that the running app has.
Thank you very much for the work. I pondered a few times how I could do that safely as I don't feel like hosting it that publicly.
I run Jellyfin publicly behind Authelia but there arent any personal files inside so if they breach it, it would give them only movies, music and tv shows...
This is excellent! Thank you!
Great work! 😎 Starred.
Please Proton team port over this UI to drive.
Material 3?
A lot more than that, especially the UX part.
Pretty cool!
Have you thought about whether this could also be used for limited write access? A common use-case for abusive image gallery services that you cannot ordinarily fulfil with Immich is shared albums where multiple people that e.g. attended the same event can collect pictures in without complex authentication (just a single shared secret or even just the link to the album).
I'd love that, too. Immich has more fine grained user control on their timeline, though.