this post was submitted on 10 May 2024
1070 points (98.4% liked)
linuxmemes
22817 readers
954 users here now
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack users for any reason. This includes using blanket terms, like "every user of thing".
- Don't get baited into back-and-forth insults. We are not animals.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, <loves/tolerates/hates> systemd, and wants to interject for a moment. You can stop now.
5. 🇬🇧 Language/язык/Sprache
- This is primarily an English-speaking community. 🇬🇧🇦🇺🇺🇸
- Comments written in other languages are allowed.
- The substance of a post should be comprehensible for people who only speak English.
- Titles and post bodies written in other languages will be allowed, but only as long as the above rule is observed.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't remove France.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
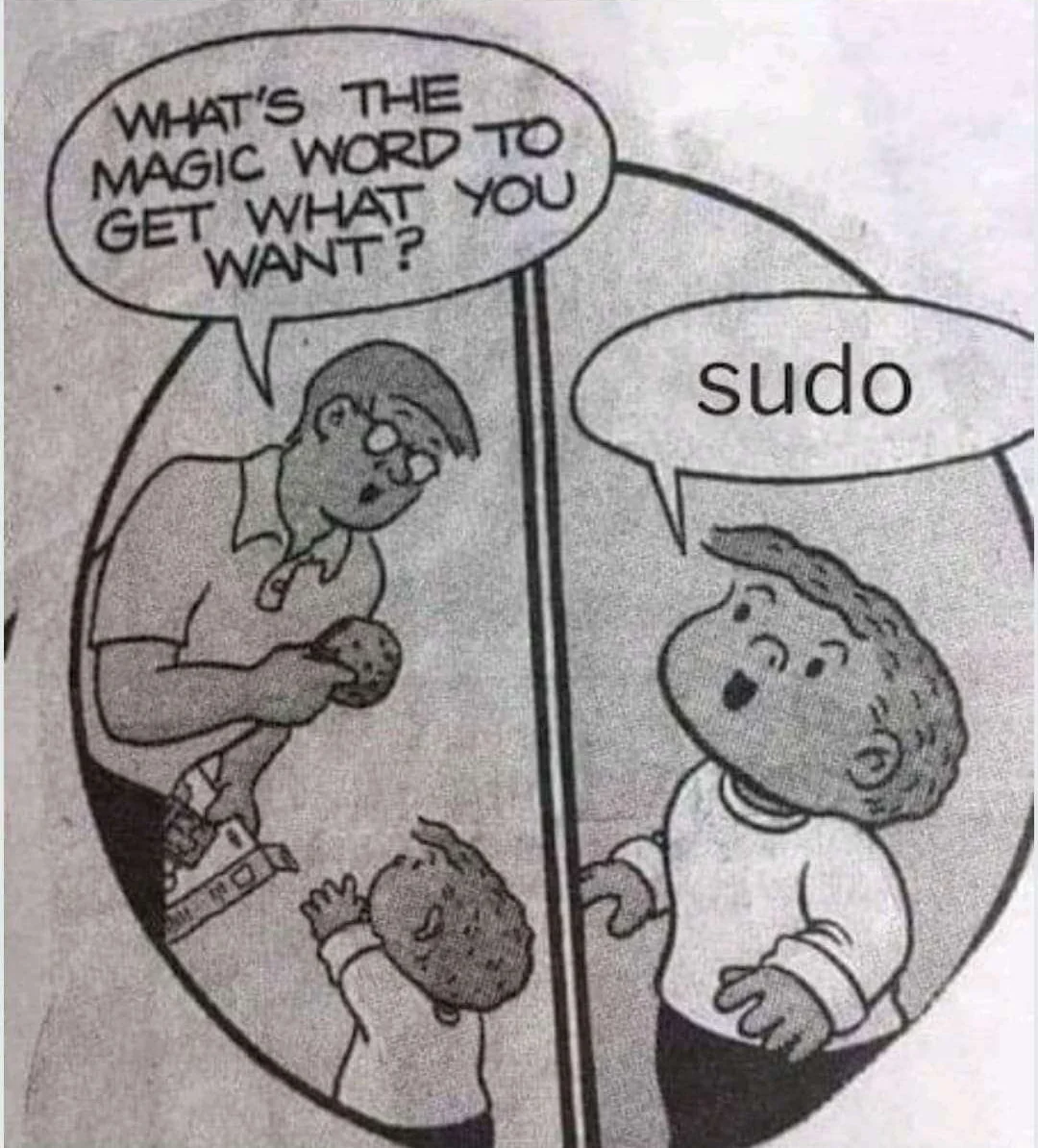
For those like me who didn't get the joke: Systemd v256 Introduces run0: A Safer Alternative to sudo / linuxiac.com
I don't know enough about IT security to understand this.
Does that mean that run0 puts programs in some form of sandbox? What's the difference now to sudo?
Basically the way sudo and doas work is that they turn your current session into a privileged one, then run the command, then put your session back the way it was, this can cause security issues. The way run0 works is that it just asks systemd to do it for you, removing those security risks.
At least thats the way I understand it, im not an expert
Someone did a ELI3 explanation for this a couple days ago. The ELI5 explanation was more complicated so someone asked for ELI3 lol
ELI3
ELI5
Sudo is a setuid binary, which means it executes with root permissions as a child of of the calling process. This technically works, but gives the untrusted process a lot of ways to mess with sudo and potentially exploit it for unauthorized access.
Run0 works by having a system service always running in the background as root. Running a command just sends a message to the already running seevice. This leaves a lot less room for exploits.
Sorry, but it's also beyond my understanding. As far as I can understand, run0 doesn't use a sandbox, but will better isolate the privileged processes from unprivileged ones when executing a command.
setuid binaries are scary, so I could see myself getting behind this.