this post was submitted on 25 Feb 2024
42 points (95.7% liked)
Linux
48413 readers
1141 users here now
From Wikipedia, the free encyclopedia
Linux is a family of open source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991 by Linus Torvalds. Linux is typically packaged in a Linux distribution (or distro for short).
Distributions include the Linux kernel and supporting system software and libraries, many of which are provided by the GNU Project. Many Linux distributions use the word "Linux" in their name, but the Free Software Foundation uses the name GNU/Linux to emphasize the importance of GNU software, causing some controversy.
Rules
- Posts must be relevant to operating systems running the Linux kernel. GNU/Linux or otherwise.
- No misinformation
- No NSFW content
- No hate speech, bigotry, etc
Related Communities
Community icon by Alpár-Etele Méder, licensed under CC BY 3.0
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
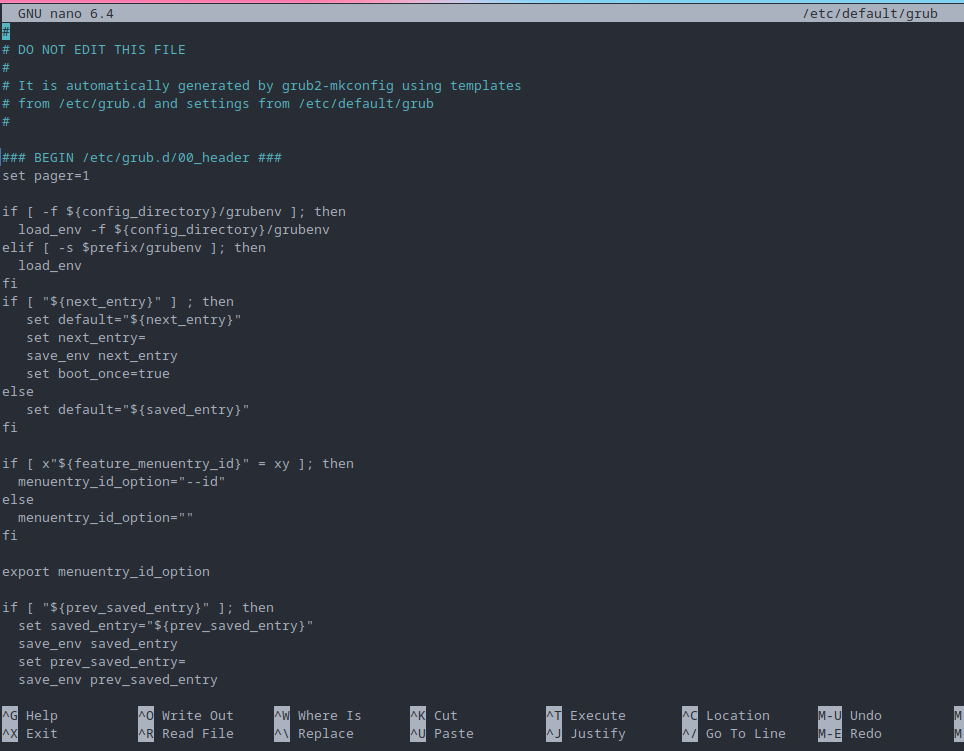
For improved security during file edits that require root access, it's highly advised to use
sudoedit(orsudo -e). This method is considered the standard practice to avoid the security pitfalls associated with directly invoking editors withsudo. To ensure the use ofnanowithsudoedit, simply set theVISUALenvironment variable withexport VISUAL=nanobefore runningsudoedit. Alternatively, for a one-off command:VISUAL=nano sudoedit /path/to/file.Please note that while
sudoeditis a safer starting point, it's not the only method available. Alternatives such asdoas,doasedit, or leveragingpolkitwithpkexeccan offer even more controlled and secure ways to manage file editing with elevated privileges. However, it's perfectly acceptable to stick withsudoedit, as it's a commonly trusted tool.Be aware that direct usage of
sudo nanoor other editors is strongly discouraged. It bypasses important security mechanisms and can lead to inadvertent system-wide risks.EDIT: changed
VISUAL=nano sudoedittoVISUAL=nano sudoedit /path/to/file.On shared systems with untrusted users, you're right. On your own system when you already have full admin rights,
sudo nanois fine and doesn't have any security implications that I'm aware of.I agree with the general sentiment. Thank you for mentioning that!
Though, the use of
sudo nanomight still pose a risk if any software found on the system is either vulnerable/exploitable, not trusted, or simply exploitative. In that case, like what's achieved through sandboxing i.e. not allow the software to go beyond their intended scope, it makes sense to put a limit on the capabilities of the software. And to that effect, the use ofsudoeditstill offers merit oversudo nano.Though, if the user doesn't (already) rely on bubblejail, firejail, Flatpak etc for what they offer in sandboxing. And/or if said user simply doesn't care for the principle of least privilege, then the use of
sudo nanois perfectly valid.This isn’t a scenario I’m familiar with. How can I learn more?